OpenID Connect is now available on Open Industrial Data (OID). When you sign up to Cognite Hub, you get an account and can access both the publicdatacdm and publicdata projects.
Whether you are new to OID or have been using API keys to access the data in this project, here’s all you need to get started with OIDC.
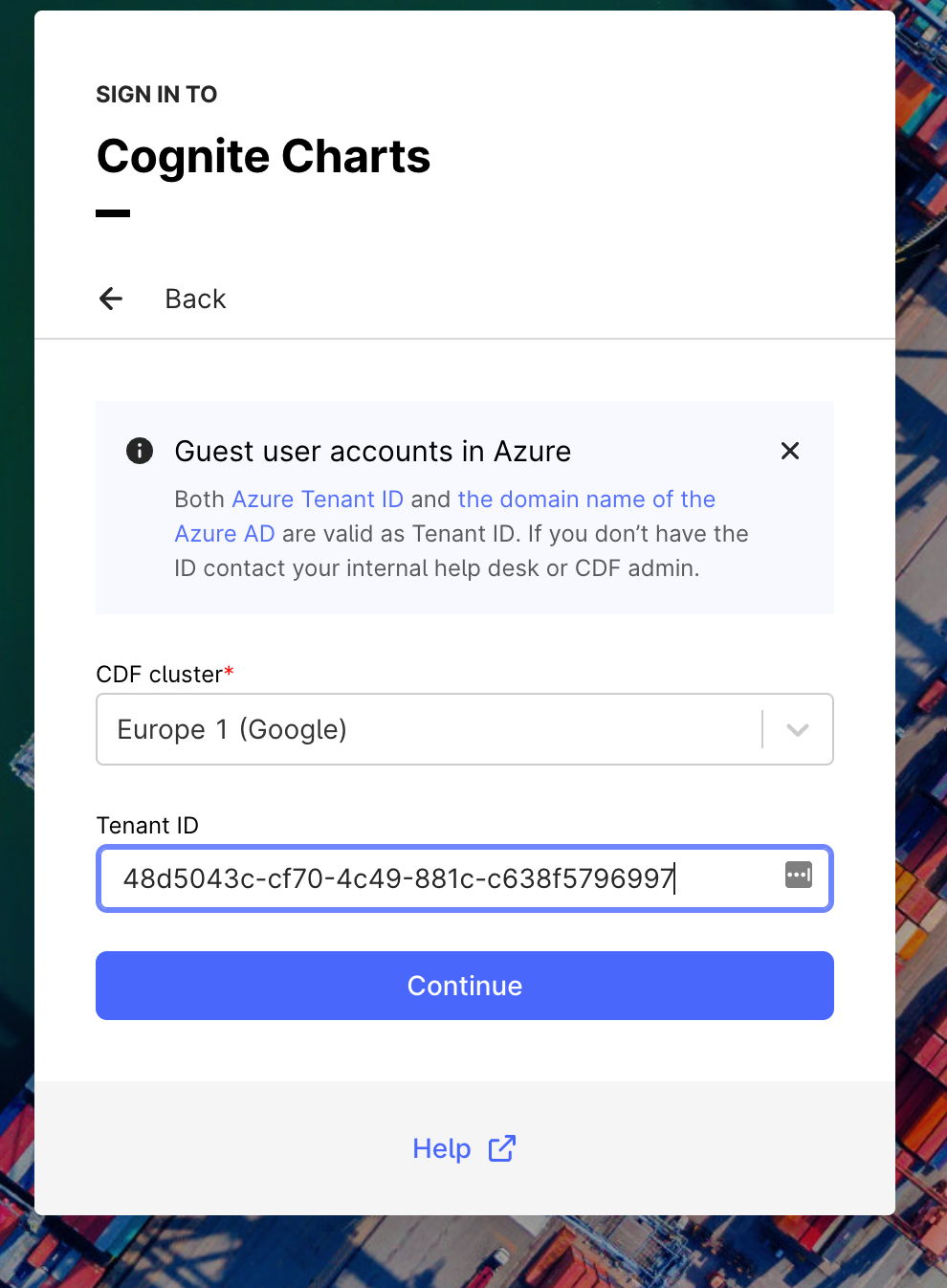
Connection Details
The credentials for each project are listed below. Please use the details corresponding to the project you wish to access.
For the publicdatacdm Project
Details for Postman and Python SDK:
-
Tenant ID:
48d5043c-cf70-4c49-881c-c638f5796997 -
Client ID:
1b90ede3-271e-401b-81a0-a4d52bea3273 -
project:
publicdatacdm -
CDF_CLUSTER:
api -
App name: OID-Api
Note: This app registration is configured with replyURLs for Postman and to run Python SDK apps locally with http/https.
Details for JavaScript Applications:
-
Tenant ID:
48d5043c-cf70-4c49-881c-c638f5796997 -
Client ID:
dea6bb8d-0f48-4bf0-a469-176fc19edc14 -
project:
publicdatacdm -
CDF_CLUSTER:
api -
App name: OID-js
Note: This app registration is configured with replyURL to run locally with http/https.
For the publicdata Project
Details for Postman and Python SDK:
-
Tenant ID:
48d5043c-cf70-4c49-881c-c638f5796997 -
Client ID:
1b90ede3-271e-401b-81a0-a4d52bea3273 -
project:
publicdata -
CDF_CLUSTER:
api -
App name: OID-Api
Note: This app registration is configured with replyURLs for Postman and to run Python SDK apps locally with http/https.
Details for JavaScript Applications:
-
Tenant ID:
48d5043c-cf70-4c49-881c-c638f5796997 -
Client ID:
dea6bb8d-0f48-4bf0-a469-176fc19edc14 -
project:
publicdata -
CDF_CLUSTER:
api -
App name: OID-js
Note: This app registration is configured with replyURL to run locally with http/https."
How to use Postman with OIDC?
We recommend that you download, install and use Postman to test API requests and verify responses.
Update authorization: https://docs.cognite.com/dev/guides/postman/#step-3-update-authorization
How to use Cognite python SDK with OIDC?
You can authenticate the Python SDK with Azure AD by using a token retrieved when a user authenticates or with a static client secret for long-running jobs like extractors.
Learn more: https://docs.cognite.com/dev/guides/sdk/python/python_auth_oidc
How to use Cognite JavaScript SDK with OIDC?
You can follow this guide on how to authenticate with JavaScript SDK
Learn more: https://docs.cognite.com/dev/guides/sdk/js/
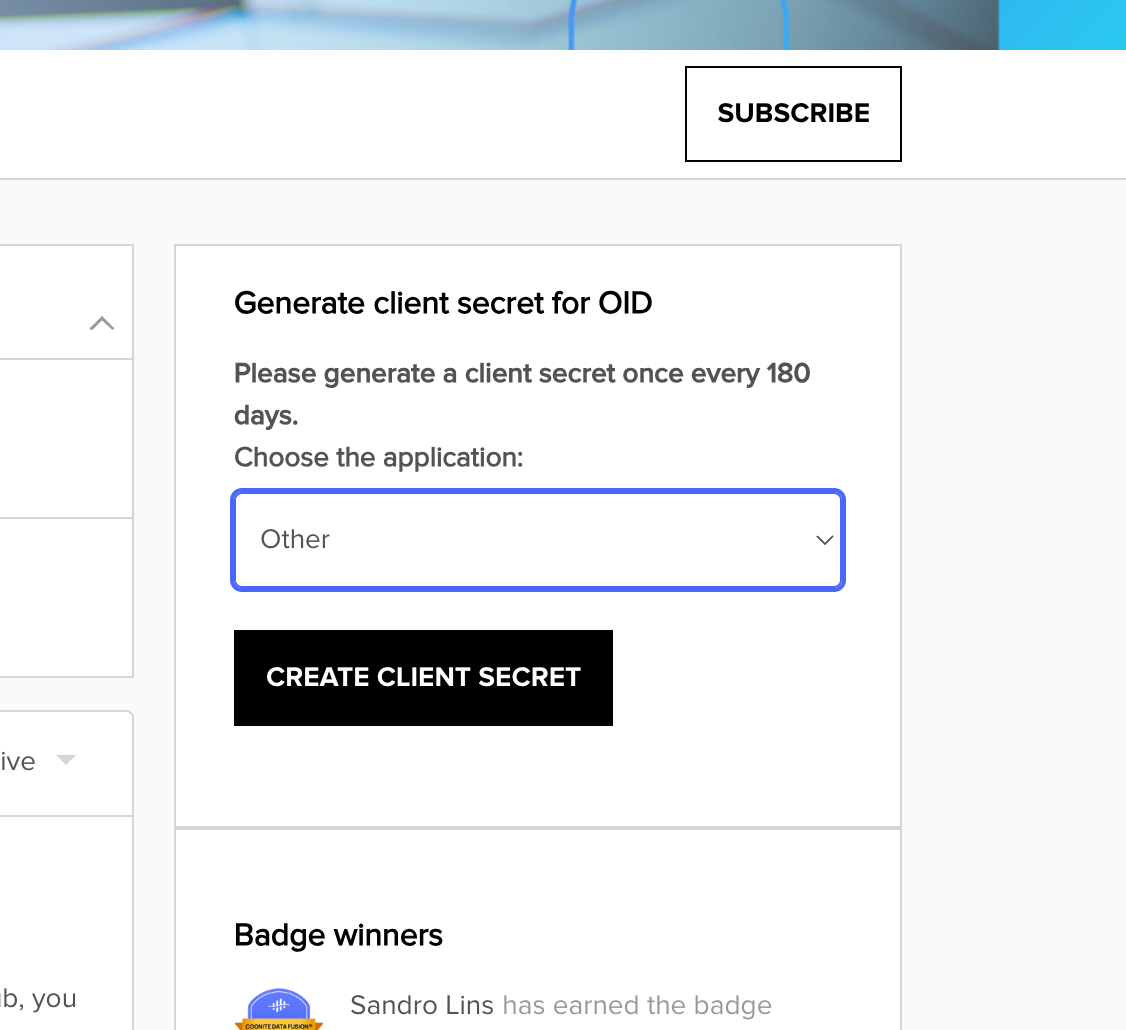
For being able to use the client credentials flow, you will need a client secret. You can generate the client secret on the following link:
How to generate a client secret for Open Industrial Data?
Let me know if you have any questions!

 Check the
documentation
Check the
documentation Ask the
Community
Ask the
Community Take a look
at
Academy
Take a look
at
Academy Cognite
Status
Page
Cognite
Status
Page Contact
Cognite Support
Contact
Cognite Support